Imagine a world where the government doesn’t need police officers to apprehend those surfers or ticket you when you violate social distancing with your girlfriend. Suppose that computers discover your beach trip by tracking your movements using a stream of information from your cell phone, your car, your GPS, facial recognition technology integrated with real-time surveillance from satellites, mounted cameras, and implanted chips. Desk-bound prosecutors or robots will notify you of your violation by text while simultaneously withdrawing your $1,000 penalty in cryptocurrency from your payroll account. Welcome to Bill Gates’ America. It’s right around the corner.
5G Strategies
Recently,
Bill Gates announced his financial support for a $1 billion plan to blanket Earth in video surveillance satellites. The company,
EarthNow, will launch 500 satellites to live-stream monitor almost every “corner” of the Earth, providing instantaneous video feedback with only a one-second delay. According to Wikipedia, the company expects its customers to include “governments and large enterprises.”
5G Antennas deploying a vast array of ground-based 5G spy antennas. Through his Bill & Melinda Gates Foundation,
Gates purchased 5.3 million Crown Castle shares currently worth a billion dollars. The Foundation’s second-largest tech holding after Microsoft, Crown Castle owns 5G infrastructure in every major U.S. market. It operates and leases more than 40,000 cell towers, 65,000 small cell nodes which are the central infrastructure for 5G and 75,000 route miles of fiber to every major U.S. market that, instead of going to your home, providing you safe, fast, wired internet, has been confiscated to connect 5G cell towers.
… 5G has almost nothing to do with improving your lives; it’s all about controlling your life, marketing products, and harvesting your data for Artificial Intelligence purposes.
Data Mining
Big Telecom, Big Data, and Bill Gates are baiting Americans into a digital tyranny-trap with million-dollar TV ads that pretend that their
multi trillion-dollar 5G investment is about faster download speeds for video games and movies. But 5G has almost nothing to do with improving your lives; it’s all about controlling your life, marketing products, and harvesting your data for Artificial Intelligence purposes.

The 21
st century’s “black gold” is data. 5G is the infrastructure for
Gates’ “Internet of Things”—a world where tens of billions of “smart” devices: cell phones, computers, automobiles, garage door openers, Apple watches, baby diapers and even our living bodies—are wirelessly interconnected to enable Big Data to gather and sell our personal information.
Gates, Elon Musk, Amazon, Facebook, and Telecom are launching the flagships for the new Gold Rush, a teeming fleet of 50,000 satellites and a network of 2,000,000 ground antennas and cell towers to strip mine data from our smart devices. This microwave radiation-emitting spider web will allow Big Data/Big Telecom and Big Brother to capture what happens inside and outside every person at every moment of life. Gates will harvest, control, sort, characterize, analyze, and sell millions of terabytes of personal information from smart devices—private health data, medical records, our shopping habits, our biometric and behavioral responses to advertising, our children’s ability to learn, our facial expressions, and conversations overheard by Siri, Alexa, and your open cell phone’s microphones. His and other corporations will use these analytics to develop
Artificial Intelligence (AI) and turn you into a predictable, easily-manipulated consuming machine.
Next time you buy a “smart” device, remember the device is not the product—you are.
Surveillance State & Transhumanism
Corporations will use Gates’ 5G surveillance system to sell products and escalate AI capacity. Governments will use it to transition the globe to a totalitarian singularity more despotic than Orwell ever imagined. Silicon Valley titans like Elon Musk, Peter Thiel, and Google’s Chief Engineer Ray Kurzweil talk longingly of “
transhumanism,” the process by which humanity will transition to become part-human, part-machine via genetic engineering and surgical implants.
Bill Gates is investing heavily to accelerate this altered reality. His ambition to tag us all with injected
subdermal vaccine data chips seems to be merely a steppingstone toward an all-encompassing surveillance state.
Rewarding Compliance
Microsoft has patented a
sinister technology that utilizes implanted sensors to monitor body and brain activity. It will reward compliant humans with crypto currency payments when they perform assigned activities.
 The Patent
The Patent,
WO |2020| 060606 has gained notoriety and the nickname “World Order 2020 666.” Microsoft describes this device as a “
Crypto Currency System” and explains that it is “capable of” using body activity data to mine bitcoin in response to compliance with assigned tasks.
People who agree to install the Microsoft harmful wireless sensors will receive periodic “duty” smart phone instructions to watch a certain advertisement, listen to a specific song, walk down a specific grocery store aisle, or to take a certain vaccine. This chip will collect data from embedded sensors that monitor brain waves, blood flow, and other body reactions. The system will transfer cryptocurrency into the subject’s account after completion of the assigned task. On the bright side, Microsoft’s dystopian invention should be a welcome source of income for the 40% of Americans put out of work by periodic COVID quarantines, by Musk’s
self-driving electronic cars, which also rely on the 5G rollout, and by Artificial Intelligence, including robots. Will Gates sell the data we freely give him to companies that will take away our jobs?
Owning Smart Cities
To consolidate his control over what people hear, learn, and think, Gates bought shares in
Liberty Global, one of the largest international television and Internet companies, operating in 30 countries and growing.
Controlling Reproduction
Gates will
even control your body, your bedroom, your medicine cabinet and even women’s menstrual and ovulation cycles. He invested approximately $18 million in
MicroCHIPS, a company that among other chip-based devices, develops birth-control implant chips with wireless on/off switches and chips for drug-delivery that allow a single implant to store and precisely deliver hundreds of therapeutic doses over months or years. The implants will be operated wirelessly by the patient to deliver medication. Knowing of Gates’ missionary
zeal for population control, however, some customers might worry that the system could be remotely activated as well.
The expansion of the wireless cloud between 2012–2015 was equivalent to adding 4.9 million cars to the roads.
Controlling Climate: Geoengineering
Cashless Society

To consolidate global control, Gates has declared war on cash, and the COVID-19 lockdowns have provided governments a convenient pretext for scuttling cash as a health hazard. Gates and his foundation are spearheading the global
shift from a cash economy towards digital transactions. Gates and Microsoft are perfectly positioned to profit from a digital payments system. By controlling digital transactions (and removing cash), Gates can control and monitor everything commercial that a country and its citizens do.
Western financial institutions—Mastercard, PayPal, Visa, eBay, and Citi—have long pushed for a cashless world. Electronic banking allows banks and financial consortiums to levy fees on every transaction.
The Digital Economy will allow the Government to monitor and scrutinize every transaction, to freeze digital accounts, and to block “financial flows” to punish disobedience. Operating in a public-private partnership with government, tech billionaires will not only control the nation but will be able to micromanage the worldwide population. Digitized currency is the ultimate instrument of social control. After all, in a cashless society, survival is impossible without access to the digitized economic system. The poor—lacking bank accounts—will suffer disproportionately.
Trillionaire Borg
While the lockdown is a cataclysm for the world economy, it is
an opportunity for Gates. By purchasing our devalued assets at a penny on the dollar, Gates’ $100 billion might make him the world’s first trillionaire. But the quarantine is also an opportunity to enlarge his power and dominion. Under Gates’ leadership, Microsoft became known as “
The Borg” because of his appetite for total market control. Now, Gates seeks to bring all humanity under his boot. His worship of technology and his megalomania threaten our freedoms, our democracy, our biology, our planet, our humanity, and our souls.
Gates’ technological dreams are not biologically sustainable. His Tower of Babel is bound to collapse, with catastrophic impact for lesser humans. It’s time to dismantle the Tower before it’s too late.

 The 21st century’s “black gold” is data. 5G is the infrastructure for Gates’ “Internet of Things”—a world where tens of billions of “smart” devices: cell phones, computers, automobiles, garage door openers, Apple watches, baby diapers and even our living bodies—are wirelessly interconnected to enable Big Data to gather and sell our personal information.
The 21st century’s “black gold” is data. 5G is the infrastructure for Gates’ “Internet of Things”—a world where tens of billions of “smart” devices: cell phones, computers, automobiles, garage door openers, Apple watches, baby diapers and even our living bodies—are wirelessly interconnected to enable Big Data to gather and sell our personal information.
 The Patent, WO |2020| 060606 has gained notoriety and the nickname “World Order 2020 666.” Microsoft describes this device as a “Crypto Currency System” and explains that it is “capable of” using body activity data to mine bitcoin in response to compliance with assigned tasks.
The Patent, WO |2020| 060606 has gained notoriety and the nickname “World Order 2020 666.” Microsoft describes this device as a “Crypto Currency System” and explains that it is “capable of” using body activity data to mine bitcoin in response to compliance with assigned tasks. Maintaining and analyzing the data collected by a 5G infrastructure require massive computers housed in major data storage complexes. To keep control of this infrastructure, Bill Gates is building his own “smart city” in Arizona. According to KPNX-TV, he spent $80 million on a 24,800-acre plot near Phoenix with the goal of turning it into a “smart city” where everything is interconnected via a wireless grid, including fleets of autonomous vehicles. The 80,000 residents of Gates’ company town will mainly work in data centers.
Maintaining and analyzing the data collected by a 5G infrastructure require massive computers housed in major data storage complexes. To keep control of this infrastructure, Bill Gates is building his own “smart city” in Arizona. According to KPNX-TV, he spent $80 million on a 24,800-acre plot near Phoenix with the goal of turning it into a “smart city” where everything is interconnected via a wireless grid, including fleets of autonomous vehicles. The 80,000 residents of Gates’ company town will mainly work in data centers.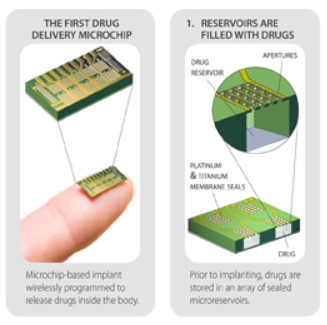 Gates will even control your body, your bedroom, your medicine cabinet and even women’s menstrual and ovulation cycles. He invested approximately $18 million in MicroCHIPS, a company that among other chip-based devices, develops birth-control implant chips with wireless on/off switches and chips for drug-delivery that allow a single implant to store and precisely deliver hundreds of therapeutic doses over months or years. The implants will be operated wirelessly by the patient to deliver medication. Knowing of Gates’ missionary zeal for population control, however, some customers might worry that the system could be remotely activated as well.
Gates will even control your body, your bedroom, your medicine cabinet and even women’s menstrual and ovulation cycles. He invested approximately $18 million in MicroCHIPS, a company that among other chip-based devices, develops birth-control implant chips with wireless on/off switches and chips for drug-delivery that allow a single implant to store and precisely deliver hundreds of therapeutic doses over months or years. The implants will be operated wirelessly by the patient to deliver medication. Knowing of Gates’ missionary zeal for population control, however, some customers might worry that the system could be remotely activated as well. To consolidate global control, Gates has declared war on cash, and the COVID-19 lockdowns have provided governments a convenient pretext for scuttling cash as a health hazard. Gates and his foundation are spearheading the global shift from a cash economy towards digital transactions. Gates and Microsoft are perfectly positioned to profit from a digital payments system. By controlling digital transactions (and removing cash), Gates can control and monitor everything commercial that a country and its citizens do.
To consolidate global control, Gates has declared war on cash, and the COVID-19 lockdowns have provided governments a convenient pretext for scuttling cash as a health hazard. Gates and his foundation are spearheading the global shift from a cash economy towards digital transactions. Gates and Microsoft are perfectly positioned to profit from a digital payments system. By controlling digital transactions (and removing cash), Gates can control and monitor everything commercial that a country and its citizens do.